XDR: the key to companies' cybersecurity

Cybersecurity is facing an increasing number of threats and, consequently, the number of tools to combat them is growing. At this point, organisations with multiple tools are finding it difficult to effectively manage multiple platforms for efficient security, and a new approach known as extended detection and response (XDR) has emerged.
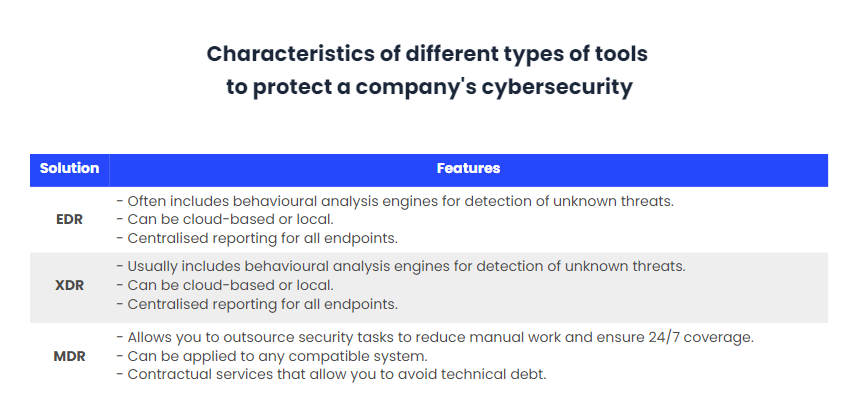
XDR claims to improve the investigation and response times of security operations centres (SOCs). As such, this new approach is emerging as an alternative to traditional reactive approaches that only provide layered visibility of attacks, such as endpoint detection and response (EDR) that had difficulty detecting complex threats.
Also, layered visibility provides a lot of information, but has problems such as a high number of alerts that are incomplete and unexplained, complex investigations to identify a breach, and tools that focus on technological weaknesses rather than the operational needs of users and companies.
XDR is a proactive approach to threat detection and response, where its visibility of data is provided across networks, clouds and endpoints while employing analytics and automating threat remediation.
What is XDR and what is it used for?
Simply put, XDR is a cross-layered detection and response tool, capable of collecting and correlating data from multiple security layers, including email, servers, applications, clouds and networks. In other words, it is an all-encompassing approach that results in visibility into the entire technology environment. This enables security teams to detect and investigate attacks faster and more effectively.
This tool focuses on collecting data in a more advanced method than previous solutions. By analysing through a constant stream of multiple events, security teams can make logical connections from a single view of data and quickly mitigate threats.
Key uses include the detection of unknown threats and advanced attacks. For these, XDR focuses security events on various controls to provide a holistic approach to the progress of complex attacks through a cross-chain of vectors. This solution transforms weak security signals from various sources into stronger signals to handle all types of threats.
Also, the tool works as an integrated platform to correlate data, thus avoiding the noise of a huge volume of security alerts. XDR discards false threats and allows operations to focus on the real threats.
How XDR security works and its characteristics
Initially, this approach is implemented as a SaaS-based tool, which must be integrated with the company’s existing products to create a unified security system. Accordingly, the system collects raw data and information from the different layers of the company’s network, generating a Data Lake, where it then performs automated analysis and correlation of the data to search for sophisticated threats.
When the tool detects a threat, it builds a graphical attack timeline, which can be accessed from a centralised user interface, generating answers on how the attack occurred, where it originated, and so on.
Finally, the tool can respond to the attack by containing or eliminating it based on correlated data available to it. In addition, XDR has threat intelligence to prevent similar threats and attacks from occurring.
XDR’s unification of the network infrastructure provides complete visibility, and this brings a number of benefits:
- Increased visibility
As already mentioned, previous versions of this type of solution focused only on one layer of security, while XDR generates a complete view of the IT infrastructure. This eliminates security silos and provides the opportunity to observe threats from anywhere, see where they originate, where they have affected, and so on. Consequently, this provides analysts with more knowledge to generate faster and more appropriate responses to the type of threat.
- Efficiency through automation
XDR uses automation to strengthen the capabilities of security staff and optimise workflows. This eliminates repetitive tasks that do not add value and waste time. In addition, this aspect enables more information to be received in a simpler way from large volumes of data so that a more efficient response can be provided.
- Increased operational quality
XDR’s view of the entire environment through centralised data collection and a single user interface improves operational efficiency. Analysts have more time to detect and remediate threats by not having to switch between dashboards depending on the tool they were using.
- Customised threat analysis
XDR’s holistic visibility allows you to tailor threat responses based on the asset under attack, leveraging control points to minimise the impact to the entire enterprise network. Previously, EDR contained compromised endpoints, which created major problems when one of the endpoints could be a critical server.
- Event classification
Automated data analysis and data correlation allows similar alerts to be grouped, prioritised and enumerated. This prevents security teams from having to deal with a large number of alerts.
- Accelerated detection and response efficiency
The generation of a Data Lake implied by this tool enables faster and more sophisticated threat detection and response, along with an increased ability to detect silent attacks.
- Improved SecOps Productivity
XDR is capable of providing an integrated incident response capability with high-fidelity alerting. It has a management centre, which as mentioned above, improves visibility into all environments. This allows low-level analysts to take on higher level threat protection roles and, as a result, increase SecOps productivity.
MDR, the next level
Managed detection and response (MDR) is the alternative being considered for the next step in such tools in cyber security, but it is still at a maturing stage. In principle, XDR and MDR employ similar approaches, both collecting and analysing data from the enterprise’s network, endpoints, servers and cloud to detect advanced threats.
Both MDR and XDR employ AI-driven data analytics and threat intelligence to drive threat visibility across platforms. However, there is a clear difference between the two tools – MDR generates a high level of human expertise around alerting data, while XDR needs people on board who know what to do with these tools in order to benefit from them.
Thus, ideally, XDR should be seen as a complement to MDR, rather than being presented as a competitor, so that it is part of a managed detection and response service. This way of working together refers to the ability for MDR providers to procure XDR sources, manage the different tools in a single approach and generate an end-to-end solution.
Finally, this next tool focuses on security outcomes and how to achieve them, unlike XDR. The outcome influences the managed component that XDR does not have and allows companies to focus on their goals instead of looking at security silos.
Players on the market
Among the various XDR service providers is Mandiant Automated Defence. A software-based analytics XDR engine within the Mandiant Advantage platform, it is able to combine human thinking with the power of AI to efficiently make complex decisions. In addition, it generates automated analytics and decision-making including network controls and data repositories and threat intelligence. This vendor includes in its XDR service:
- Built-in security expertise.
- Mandiant’s customer-specific threat intelligence.
- The ability to process millions of alerts in real time.
- Enterprise scale at machine speed.
- Continuous learning and adaptability.
- 24/7 automated monitoring of security alerts.
- Analysis, reasoning and decision making on alerts.
Another service provider comes from the combination of Carbon Black’s teams with VMware, creating a SaaS platform that provides anti-virus, threat scanning and vulnerability management capabilities from a single central platform. It also adds the integration of more VMware products such as Workspace One, vSphere and NSX Service-defined Firewall, among others. Features include:
- Detection and prevention of advanced threats.
- Knowledge of the timeline of an attack.
- Reduction of the time required to resolve a threat through automation.
- Security extended to the cloud.
- Multi-point decision making.
- Provides security teams with context from other domains for decision making when investigating a threat.
Conclusions
Until now, layered security of a corporate network has worked well, but today’s threats are more advanced and complex. In recent times, XDR has become one of the fast-growing market segments in cyber security, as this tool addresses key requirements for threat detection and response through unified analysis.
Companies will no longer require multiple products with unique solutions, as XDR is developed to address this challenge regardless of whether the threat is on an endpoint, in the network or in the cloud. XDR unifies standardises, analyses and prioritises simultaneously in an automated way.
In parallel, many organisations are turning to MDR to address the need for people who know what to do with tools like XDR or EDR to leverage them. MDR provides access to external analysts who have extensive XDR expertise to provide a great security service and comprehensive responses.
Finally, a number of vendors offer XDR SaaS services depending on the needs and sizes of enterprises. Generally, they are characterised by extended capabilities on the integration of the tool, although many still need to mature to offer a fully effective analytics service.


