SMB Security Outsourcing Trend Gains Steam
Larger businesses have been outsourcing aspects of their IT security operations for decades. This had not been the case for smaller businesses until just the last few years. Aside from using third-party network security monitoring services, the large majority of SMBs have relied on their in-house IT teams for almost all of their security needs.
The advent of the cloud, and the growing realization of their vulnerability and the consequences of a security failure among SMB owners and managers, has led to a growing interest in security services among small businesses. According to Symantec’s 2013 Avoiding the Hidden Costs of the Cloud report, more than 90% of SMBs were at least discussing moving some services to the cloud, and over 80% of the 3000+ SMBs surveyed were actively considering email management or security management via the cloud.
Image by osde8info.
Cloud Security Trends
Global spending on cloud security services is expected to expand by almost 40% between 2012 and 2016. Access Markets International Partners reports that cloud security spending topped $3.3 billion in 2012, representing 17 percent of the total IT security market. That amount is expected to increase to $7.7 billion in 2016, representing 24% of the security market.
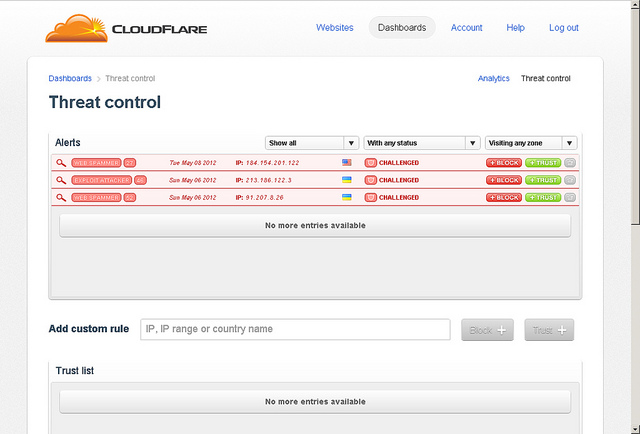
Small businesses are adopting various cloud-based security-as-a-service offerings relatively rapidly. The flexibility to mix and match services to meet individual customer needs is a big plus, and most businesses find cloud-based offerings offer significant long-term savings compared to keeping all security functions in-house. It is therefore not really surprising that SMBs are increasingly passing off security functions such as messaging and email protection, web security, data loss prevention and encryption and authentication to cloud-based providers.
More comprehensive platform-as-a-service and infrastructure-as-a-service security offerings are growing in popularity among medium-sized businesses, typically providing more security functionality at a lower price with much less management required. However, it is also important to keep in mind that cloud-based security offerings only represent a limited subset of the total business IT security needs of most businesses.
Determining What Security to Outsource
The first step in getting a real grip on what security functions you can/should outsource is to develop a thorough understanding of your business and your security needs. You need to rationally categorize your security needs, decide what you are going to keep in-house, and then thoughtfully examine your options regarding which functions to outsource and what provider to use. Most IT experts advise that security is not the place to cut corners on your IT budget, and that it is generally worth paying a little extra to work with a well-regarded industry provider.
Switching from in-house email and web security to using a cloud-based provider is pretty straightforward, and is certainly within the purview of a reasonably competent IT professional. But if you are making a major security upgrade or are undertaking business-transforming initiatives, it might be a good idea to work with a value-added reseller or bring in a security consultant.
For larger security initiatives, the final step -- contract negotiations -- is potentially the trickiest step in the whole process. This is especially true if you are not working with an experienced consultant. Key issues to make sure to consider in contract negotiations include ownership or leasing of hardware, software licenses, employee transfer, intellectual property, audit rights, billing, recourse and remediation, as well as terms for renewal or termination of services. It is also critical to thoroughly investigate any potential conflicts of interest before you get to the final stages of contract negotiations.



